Medical Devices Caught Taking Patient Information Without Consent
Imagine sitting in the cafeteria at Central High, nibbling on your sandwich, and suddenly a tech-savvy teacher starts schooling everyone about “medical devices data privacy violations.” It sounds like something out of a sci-fi thriller, but it’s a reality we’re living in today. With personal information at stake, from our simplest emails to the most critical medical records, understanding how these data breaches occur is crucial for entrepreneurs and small business owners. Let’s explore how our everyday tech and healthcare devices might be spilling more than just the beans.
AI Automation & IT Services with a Twist
Just like how Amazon is tightening its cyber defenses by bolstering its Redshift service, ensuring it encrypts data and blocks unwanted public access, businesses can take notes on this. It’s a practical move towards enhancing data security, which is crucial not just for tech giants but also for smaller firms dipping their toes into AI projects. But how do you keep these projects safe while ensuring smooth operation? Think of private clouds akin to a secret clubhouse – they keep your digital affairs protected and swift. This is a lesson in privacy well worth adapting to protect against any medical devices data privacy violations.
Cybersecurity: A Sneaky Business
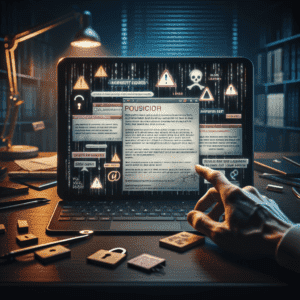
Ms. Lopez, in our high school tale, wasn’t just hyperbolic when she warned about security flaws in healthcare devices. Real-world examples like Contec’s patient monitors, which were taken offline due to such breaches, showcase the gravity of these threats. It’s similar to someone nabbing your open locker’s contents—only here, it’s sensitive patient information up for grabs. Even Dell had its share of security fixes to implement, exhibiting that breaches are not just a minor nuisance but a potential catastrophe waiting to unfold.
Consider software threats like TorNet, a cunning malware that tricks users into interacting with fake emails, wreaking havoc on computers across Germany and Poland. It’s like the digital version of a home invasion catch – silent but devastatingly effective.
When Backdoors Come Knocking
The analogy Ms. Lopez used about leaving your locker wide open resonates here. A hospital in Connecticut learned this lesson the hard way when a data breach affected millions. The institution is now enhancing its security blueprint. It’s a stark reminder of the need for immediately assessing and addressing vulnerabilities.
Data Breach Incidents That Rattle the Bones
When big names like MGM Resorts and Volkswagen face data breaches, the ripple effect is significant. MGM is forking out $45 million due to leaks that didn’t just expose the common visitor but also celebrities. Imagine waking up to find out your information is public. This situation underlines why medical devices data privacy violations aren’t a far-fetched fear but a significant risk that could affect everyone, from hotels to healthcare.
Similarly, no one would expect Volkswagen‘s electric vehicles to spill data, yet here we are. The reality is that breaches can happen to anyone, including beloved brands like the publisher of the Harry Potter series, which also grappled with an unexpected data leak.
Privacy Concerns in Business & Legal Spheres
In the world of privacy and legal mats, services like Cloudflare have been questioned for potentially exposing user locations. Such concerns reverberate through all levels of business, pressing entrepreneurs to scrutinize and strengthen the cybersecurity of their platforms. Meanwhile, in the UK, there’s a push towards better government cybersecurity to avoid delays in protection. It’s a clarion call for small biz owners: secure now to avoid more significant headaches later.
Stay Smart on Social Media Marketing
Lastly, the world of social media marketing thrives on innovation but not without a robust security fortress. As with Sarah’s blunder of clicking on sketchy links, it’s a cautionary tale of what not to do. Entrepreneurs need to educate themselves and their teams on the potential pitfalls—like the dangers of digital breadcrumbs leading nefarious entities back to your precious data.
Conclusion: Strong, Stealthy, Secure
Just like Jake promising to switch up his weak passwords, our strategic cyber habits can safeguard us against the menace of medical devices data privacy violations. As entrepreneurs and small business owners, weave a tapestry of security measures: robust passwords, careful vigilance, regular updates, and a savvy approach to digital traps. Remember, our devices are like lockers filled with valuable information; keep them locked tight to prevent any unwanted secrets from slipping out.